Architecting, developing and deploying enterprise IT solutions.
Learn More











STPAbout specializes in buildingServices IT infrastructures and state of the art cybersecurity systemsThe IRS & STP.
Case Studies
For over 15 years, customers have called upon STP to build their mission critical IT systems.

Designing for the Future
STP’s engineers successfully integrated Equifax’s proprietary KBA service with eAuthentication’s proprietary commercial off-the-shelf (COTS) identity proofing software.
- Application Development
- Cybersecurity
- Engineering

Ensuring Continuity of Service
Working through a Unisys contract, STP engineers, project managers and subject matter experts were tasked with devising a strategy, managing the plan, and implementing the solution to keep the infrastructure up and running, 24×7, 365 days a year.
- Engineering
- Infrastructure

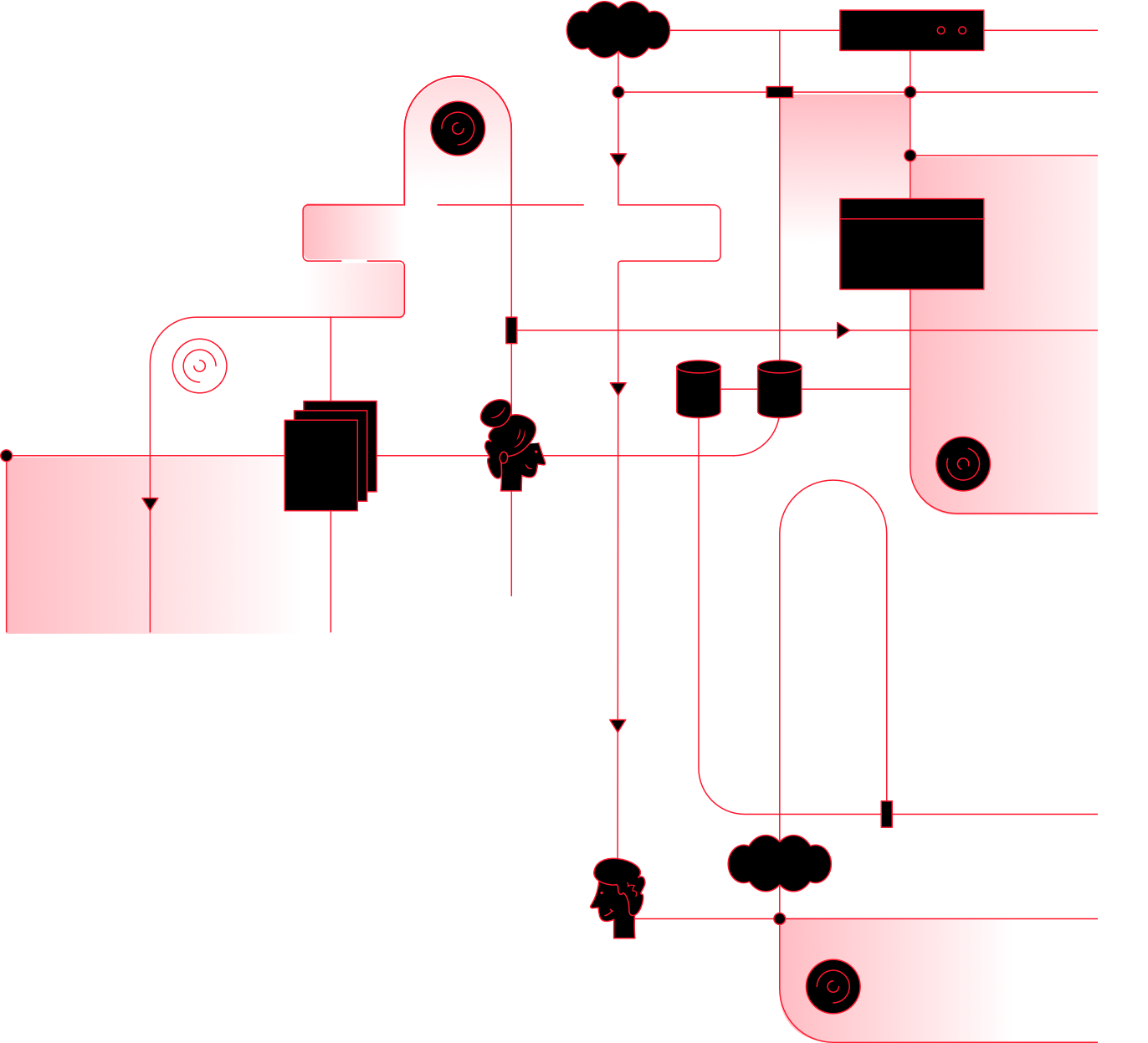
Building an End-to-End Software Distribution Workflow for the Enterprise
Based on DevOps principles, STP engineers working in conjunction with the IRS developed the Deploy and Release Integration and Visibility Engine (DRIVE).
- Automation
1.1m Purchased hours of STP expertise.
156 STP personnel who have worked on federal contracts.
43m People have used systems that we built.